By Nic Lindh on Sunday, 19 October 2014
The state of technology these days is incredible—we have a world-wide instant communications network accessible to the majority of people living in developed countries (and spreading fast to the rest of the world); we are able to carry devices in our pockets that connect to the global network and sense where we are and what we are doing; we have covered the sky in satellites. Think about that: We put man-made objects in orbit and they perform duties for us all day every day. It’s mind-boggling.
But.
It’s all duct tape, bailing wire and custom code all the way down.
Hardly a day goes by without some security vulnerability hitting one of the pieces of software we depend on. Target, Home Depot and who knows who else have leaked customer credit cards. Heartbleed, Poodle and Shellshock have exploited old, old bugs lurking in the foundations of the code that runs our entire online civilization. Flash and Microsoft Word—just to provide high-profile examples—keep releasing security updates for horrific vulnerabilities that would allow anybody to control your computer and see all your data from anywhere in the connected world.
That’s a plugin that plays videos and a word processor. They are leaky enough that somebody could use their flaws to control your computer. You should be asking yourself why either of these programs have enough access to your computer this is even possible.
Massive vulnerabilities are just background noise at this point.
Back in a previous life I worked with a bunch of electrical engineers who explained to me at a very high level suitable for a dummy how a computer actually works. Ever since, I’m slightly gratified any time one of them actually boots and works. The complexity is mind-blowing. It really is. Seriously, if you’re physically close to a university, roll by and buy a few engineering students some coffee and/or beer and have them explain this stuff to you. You will never believe your phone will work right again.
Now think about software. Whether you have an Android or iOS device, you probably enjoy using it. The software is nice and lets you do what you want with a minimum of headaches. Now think about your job. If you work for any kind of large or specialized organization, you get to use custom software.
How is that going for you?
Most likely it’s terrible. Turns out, writing software is really hard and the big companies like Adobe, Apple, Google and Microsoft expend an incredible amount of effort and spend a ton of money hiring the smartest people possible to make that happen.
Most companies do not have that kind of talent pool or that kind of resources. They still write software. And most of it is terrible. Because, again, software is hard and most people will do a terrible job of writing it.
That’s the custom order system that makes you want to stab somebody at work every day.
But not only can’t “normal” people write good software: The exploits that are coming out all the time are against the best code we, as a species, can write. The smartest people with the most experience are writing code with horrible vulnerabilities. Not because they’re not good at their jobs—they are. But because we humans are not capable of explaining things to computers, at least not the way we’re doing it now.
This whole problem used to not be that big a deal when it was mostly nerds talking about Star Trek on the Global Network, but now it’s tied in to everything, including the status of your retirement account and how much money is owed on your credit card.
And soon, your house, your refrigerator, the power grid and your car will be controlled by a system that is full of holes.
Do you enjoy knowing that soon your car will be vulnerable to some sociopathic griefer taking out the brakes for lulz?
So apart from fear mongering, what can be done? We really, really need to make it a priority to shore up our basic infrastructure and to realize that humans just can’t write safe C and assembly code. We don’t have the wiring for it. No matter how smart you are, you will screw up. And then some hacker will take control of a nuclear power plant and things go from bad to horrible.
We have to get away from C and assembly. But that would mean a lot of billion-dollar companies stopping what they’re doing and ignoring Wall Street for as long as it takes to retool from the ground up. Odds of that happening? Well, Ghostrider, that would be a zero.
It’s going to get worse, much worse, before it’s done.
Hope you have a diesel generator.
Oh, and you should totally invest in a hockey mask.

Let’s talk about how fun it is to have a go-cart people mover.
Is there reason to upgrade from a 3 to a 5?
The Internet tells Nic to install Ubiquiti gear in his house, so he does, and now he has thoughts.
What I wish I’d known when I started podcasting.
Nic reports his experiences so far with voice computing from Amazon and Google and is a bit mystified at the reaction to Apple’s HomePod.
After a few weeks of using iPhone X I’m ready to join the congratulatory choir.
Nic is interested in smart homes. His contractor let him know how the wealthy are already using them.
A concise guide to getting started with podcasting, including equipment, editing, mic technique and hosting.
Apple’s neglect of the pro market is causing a lot of gnashing of teeth in Apple-nerd circles, but it’s true to Apple’s vision.
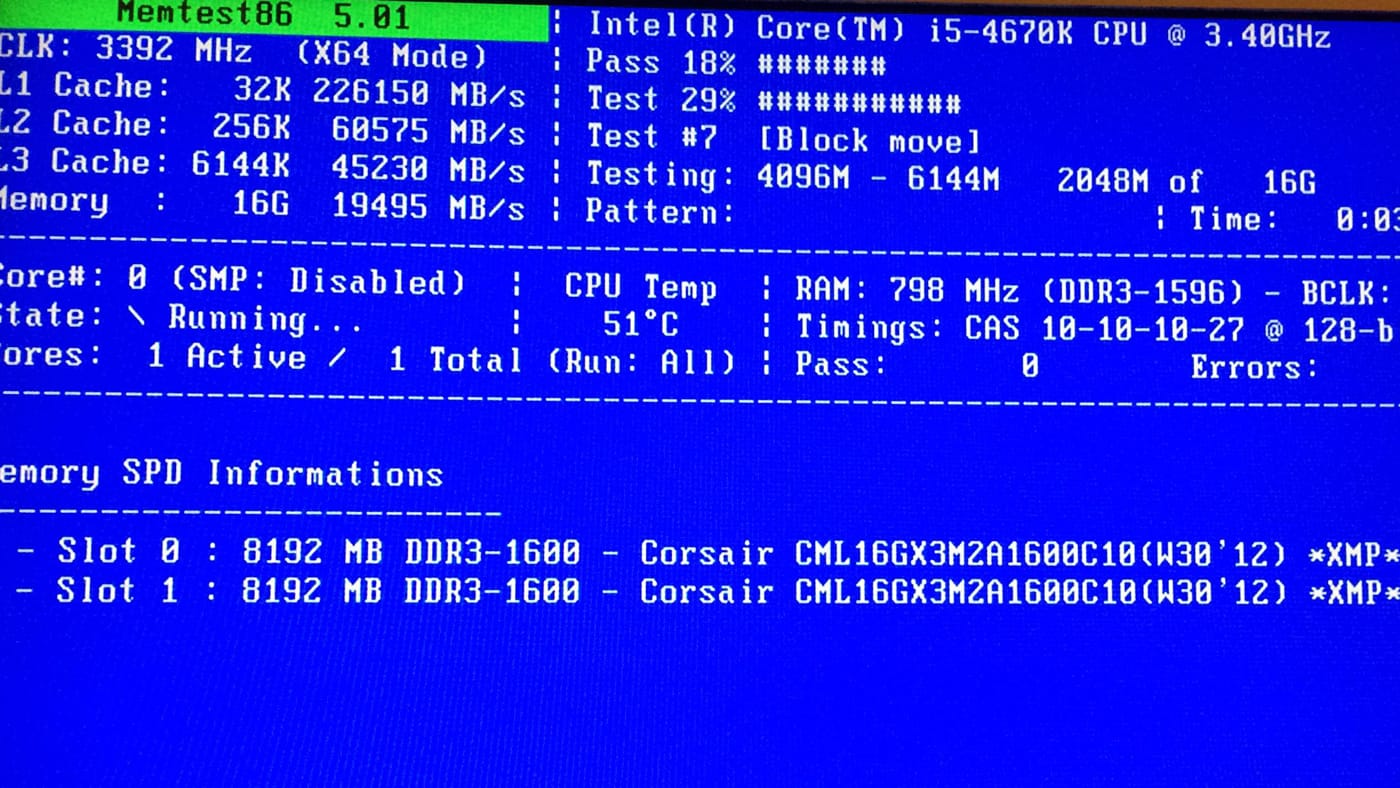
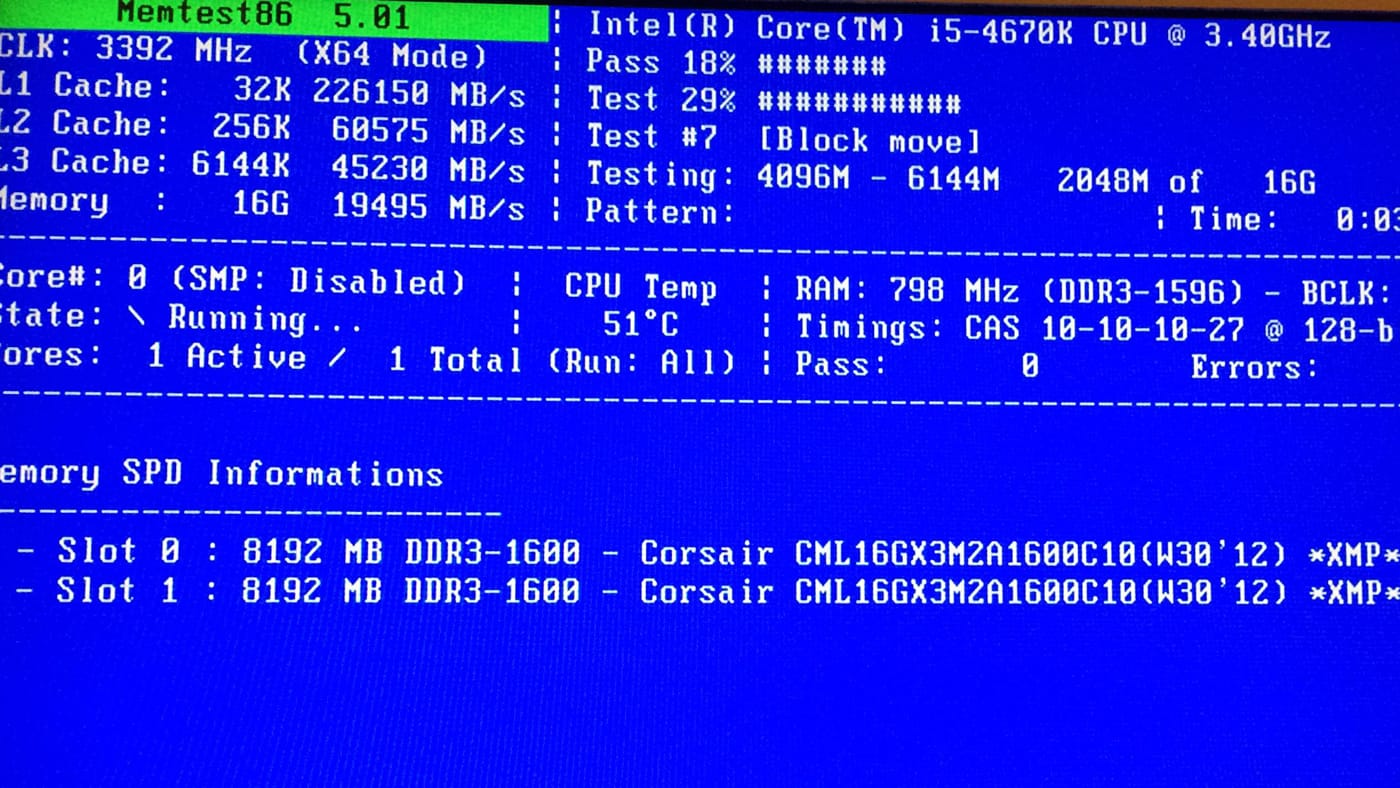
There is unrest in the Mac community about Apple’s commitment to the platform. Some are turning their eyes to building a Hackintosh to get the kind of computer Apple doesn’t provide. Here’s what it’s like to run a Hackintosh.
Car nerds are dealing with some cognitive dissonance as car technology changes.
The Oasis is Amazon’s best e-ink reader to date, but it’s not good enough for the price.
Nic buys an Amazon Echo and is indubitably happy with the fantasy star ship in his head.
The problem isn’t ads. The problem is being stalked like an animal across the internet.
The DS416j is a nice NAS for light home use. Just don’t expect raw power.
The Core Dump is moving to GitHub Pages. This is a good thing, most likely.
Thoughts on Apple Watch after half a year of daily usage.
Predictably, the Paris attacks brought the anti-encryption crowd back out of the woodwork. They're at best being willfully disingenuous.
Things to consider when planning to build a site on a compressed time table.
Nic provides some basic not-too-paranoid tips for securing your digital life.
Installing Jekyll on an EC2 Amazon Linux AMI is easy. Here are the steps.
After wearing the watch for over a month, Nic has thoughts on its future. Spoiler: Depends on how you define success.
Turns out “it's just a big iPhone” is a stroke of genius.
Some technical terms still confuse people who should know better, like journalists.
How to host a static site on Amazon S3 with an apex domain without using Amazon’s Route 53.
People fear change, so new technology is used as as a faster version of the old. This makes technologists sad.
Nic provides a lesson plan for teaching total beginners HTML, CSS and JavaScript.
Nic loves his Pebble and looks forward to the Apple Watch, but realizes he’s in the minority.
Nic loves books, but he loves their content more.
Nic tries to understand the WATCH. It doesn’t go well.
Nic thinks home integration could be Apple’s next major category. Read on to find out why.
Nic is frustrated with his Kindle and would love to see Apple make an e-ink reader.
Nic delves into the shady computer enthusiast underworld of the Hackintosh.
On the Mac’s 30th anniversary, Nic reminisces about his first.
The iPhone was announced Jan. 9, 2007. It now occupies a huge chunk of Nic’s life.
Nic is very impressed with the speed of the iPhone 5S and iPad Air.
Nic tells you how to find a theme for your new site.
Nic buys a Nexus 7 to test the Android waters.
All Nic wants for WWDC is sync that actually works
Nic is ecstatic about the backlighting on the Kindle Paperlight, but Amazon has made some strange design decisions and there’s a display hardware flaw.
Nic makes a new ebook and is dismayed by the sad state of ebook publishing.
One of the equivalences of haircut and clothing on the Internet is your email address.
Nic outlines some of the risks of ceding comments on news stories to Facebook.
Nic is bemused by the sturm und drang surrounding the iOS-ification of Mac OS X.
Web publishing used to require heavy-duty nerditry, but no longer.
Nic is creating an e-book. He shares what he’s learned so far.
Nic really digs e-book readers. No, seriously, he really digs them. And you should, too.
The future and now of personal computing is appliances. This post parses why you shouldn’t worry about it.